Putty command line options for ssh 78 4
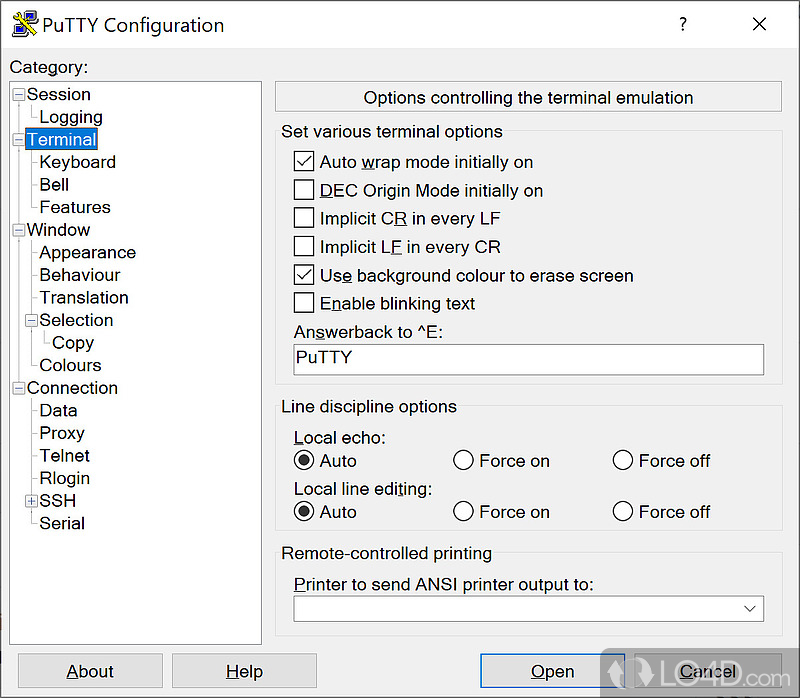
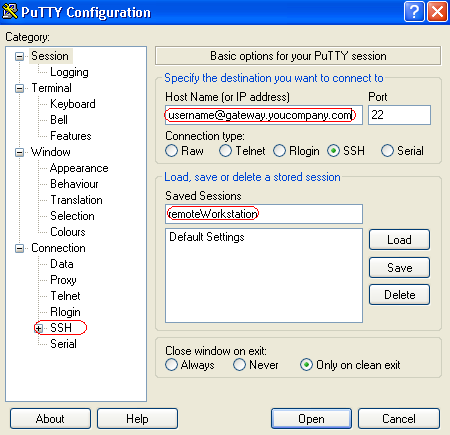
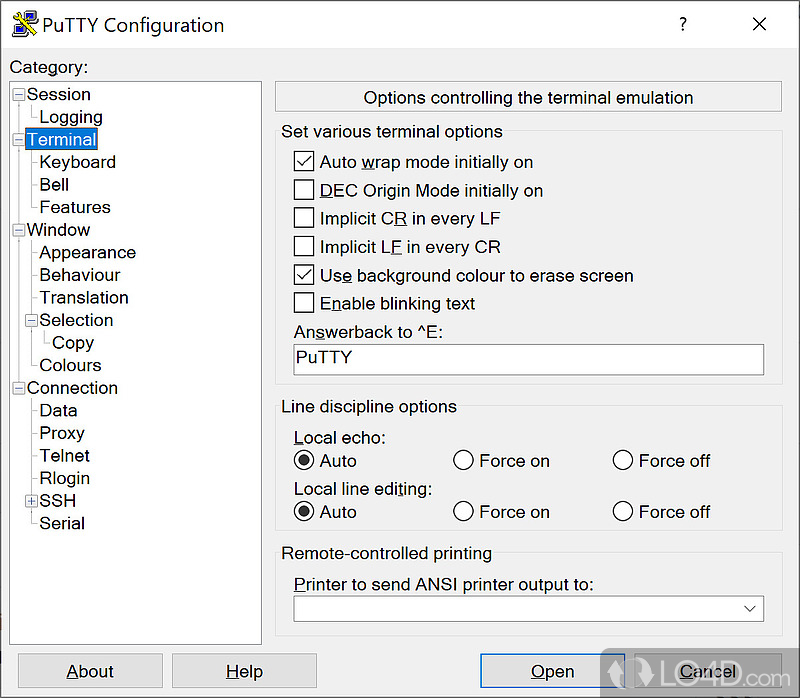
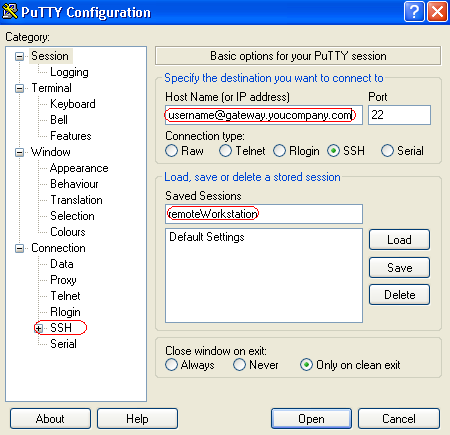
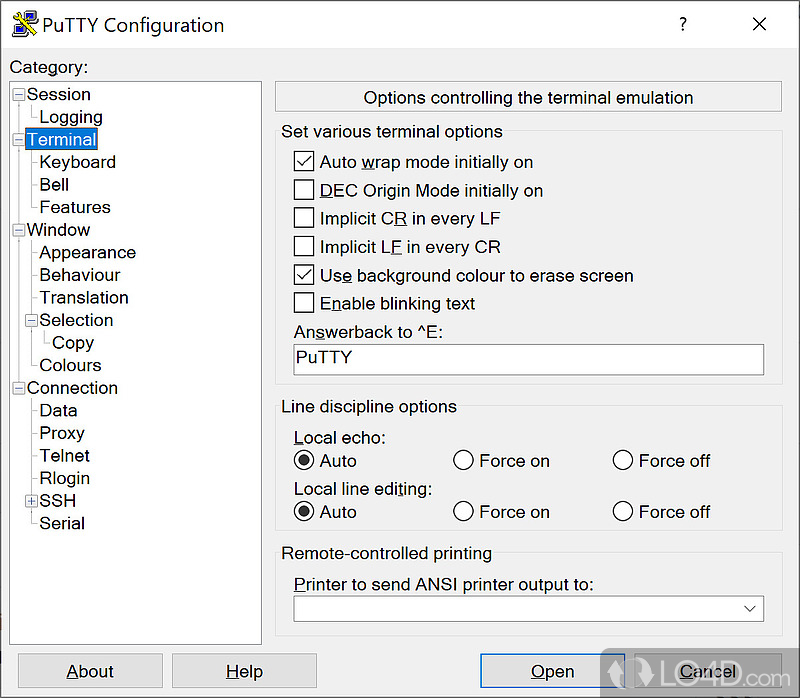
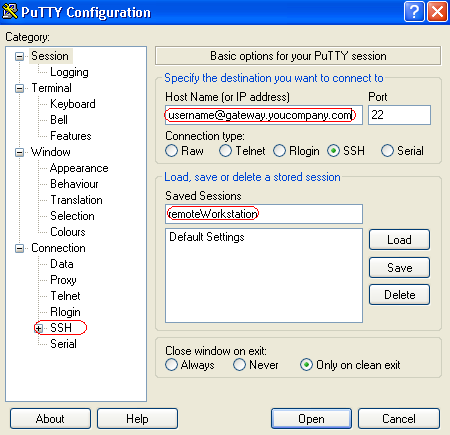
Home FAQ Feedback Licence Updates Mirrors Keys Links Team Download: These protocols are all used to run a remote session on a computer, over a network. PuTTY implements the client end of that session: In really simple terms: PuTTY opens a window. Then, anything you type into that window is sent straight to the Unix machine, and everything the Unix machine sends back is displayed in the window. So you can work on the Unix machine as if you were sitting at its console, while actually sitting somewhere else. In general, if you want to know if PuTTY supports a particular feature, you should look for it on the PuTTY web site. PuTTY doesn't support this natively see the wishlist entry for reasons why notbut as of 0. However, the SSH-1 protocol has many weaknesses and is no longer considered secure; you should use SSH-2 instead if at all possible. New in version 0. If you have a problem with Ssh default choice, you can force each option to be options or disabled as you choose. Yes, all of PuTTY's settings can be saved in named session profiles. You can also change the default settings that are used for new sessions. Not at present, although section 4. Remembering your password is a bad plan for obvious security reasons: In addition, it's not even possible for PuTTY to automatically send your password in a Telnet session, because Telnet doesn't give the client software any indication of which part of the login process is the password prompt. In SSH, remembering your password would be possible in theory, but there doesn't seem to be much point since SSH supports public key authentication, which is more flexible and more secure. See chapter 8 in the documentation for a full discussion of public key authentication. And there won't be. Even if you write it yourself and send us the patch, we won't accept it. Those annoying host key prompts are the whole point of SSH. Without them, all the cryptographic technology SSH uses to secure your session is doing nothing more than making an attacker's job slightly harder; instead of sitting between you and the server with a packet sniffer, the attacker must actually subvert a router and start modifying the packets going back and forth. But that's not all that much harder than just sniffing; and without host key checking, it will go completely undetected by client or server. Host key checking is your guarantee that the encryption you put on your data at the client end is the same encryption taken off the data at the server end; it's your guarantee that it hasn't been removed and replaced somewhere on the way. Host key checking makes the attacker's job astronomically hard, compared to packet sniffing, and even compared to subverting a router. Instead of applying a little intelligence and keeping an eye on Ssh, the attacker must now perform a brute-force attack against at least one military-strength cipher. That insignificant host key prompt really does make that much difference. If you're having a specific problem with host key checking - perhaps you want an automated batch job to make use of PSCP or Plink, and the interactive host options prompt is hanging the batch process - then the right way to fix it is to add the correct host key to the Registry in advance, or if the Registry is not available, to use the -hostkey command-line option. That way, you retain the important feature of host key checking: Adding an option to turn host key checking off completely is the wrong solution and we will not putty it. REG file, which can be installed ahead of time by double-clicking or using REGEDIT. The only reason we might want to would be if we could easily re-use existing code and significantly cut down the effort. We don't believe this is the case; there just isn't enough common ground between an SSH client and server to make it worthwhile. If someone else wants to use bits of PuTTY in the process of writing a Windows SSH server, they'd be perfectly welcome to of course, but I really can't see it being a lot less effort for us to do that than it would be for us to write a server from the ground up. We don't have time, and we don't have motivation. The code is available if anyone else wants to try it. Until recently, this was a limitation of the file transfer protocols: This is still true of SCP. The current draft protocol spec of SFTP proposes a means of implementing ASCII transfer. The eventual goal is for PuTTY to be a multi-platform program, able to run on at least Windows, Mac OS and Unix. Porting will become easier once PuTTY has a generalised porting layer, drawing a clear line between platform-dependent and platform-independent code. The general intention was for command porting layer to evolve naturally as part of the process of doing the first port; a Unix port has now been released and the plan seems putty be working so far. We provide bit and bit Windows executables; see question A. We used to also provide executables for Windows for the Alpha processor, but stopped after 0. In the development code, a partial port to Mac OS exists see question A. Currently PuTTY does not run on Windows CE see question A. We do not have release-quality ports for any other systems at the present time. If anyone told you we had an Android port, or an iOS port, or any other port of PuTTY, they were mistaken. There are some third-party ports to various platforms, mentioned on the Links page of our website. If you look at the source release, you should find a unix subdirectory. This should build you Unix ports of Plink, PuTTY itself, PuTTYgen, PSCP, PSFTP, Pageant, and also pterm - an xterm -type program which supports the same terminal emulation as PuTTY. If you don't have Gtk, you should still be able to build the command-line tools. All sorts of little things. Unix Plink has apparently found a niche among people who find the complexity of OpenSSL makes OpenSSH hard to install and who don't mind Putty not for as many features. Some users want to generate a large number of SSH keys on Unix and then copy line all into PuTTY, and the Unix PuTTYgen should allow them to automate that conversion process. There were development advantages as well; porting PuTTY to Unix was a valuable path-finding effort for other future ports, and also allowed us to use the excellent Linux tool Valgrind to help with debugging, which has already improved PuTTY's stability on all platforms. We don't expect our Unix port to be the right thing for everybody. We once did some work on such a port, but it only reached an early stage, and certainly not a useful one. It's no longer being actively worked on. PuTTY is a bit application from the ground up, so it won't run on Windows 3. However, it is possible in theory to compile the existing PuTTY source in such a way that it will run under Win32s an extension to Windows 3. In order to do this you'll need the right kind of C compiler - modern versions of Visual C at least have stopped being backwards compatible options Win32s. Also, the last time we tried this it didn't work very well. We attempted one aroundwritten as a native Cocoa application, but it turned out to be very slow to redraw its window for some reason we never got to the bottom of. Inafter porting the GTK front end to work with GTK 3, we began another attempt based on making small changes to the GTK code and building it against the OS X Quartz version of GTK 3. This doesn't seem to have the window redrawing problem any more, command it's already got further than the last effort, but it is still substantially unfinished. I hope so, but given that ports aren't really progressing very fast even on systems the developers do already know how to program for, it might be a long time before any of us get round to learning a new system and doing the port for that. However, some of the work has been done by other people; see the Links page of our website for various third-party ports. We have no plans to write such a port ourselves; none of us has an iPhone, and developing and publishing applications for it looks awkward and expensive. This is nothing to do with our similarly-named ptermwhich is a standalone terminal emulator for Unix systems; see question A. It would take a reasonable amount of rewriting for this to be possible, and since the PuTTY project itself doesn't believe in DLLs they make installation more error-prone none of us has taken the time to do it. Most of the code cleanup work would be a good thing to happen in general, so if anyone feels like helping, we wouldn't say no. None of the PuTTY team uses Visual Basic, and none of us has any particular need putty make SSH connections from a Visual Basic application. In addition, all the preliminary work to turn it into a DLL would be necessary first; and furthermore, we don't even know how to write VB components. If someone offers to do some of this work for us, we might consider it, but unless that happens I can't see VB integration being anywhere other than the very bottom of our priority list. Probably your best bet is to use Plink, the command-line connection tool. If you can start Plink as a second Windows process, and arrange for your primary process to be able to send data to the Plink process, and receive data from it, through pipes, then you should be able to make SSH connections from your program. PuTTY also supports some terminal control sequences not supported by the real xterm: By default, PuTTY announces its terminal type to the server as xterm. If you have a problem with this, you can reconfigure it to say something else; vt might help if you have trouble. On Windows, PuTTY stores most of its data saved sessions, SSH host keys in the Registry. The precise location is. PuTTY also requires a random number seed file, to improve the unpredictability of randomly chosen data needed as part of the SSH cryptography. This is stored by default in a file called PUTTY. If you want to change the location of the random number seed file, you can put your chosen pathname in the Registry, at. PuTTY is a communications tool, for making connections to other computers. We maintain the tool; we don't administer any computers that you're likely to be able to use, in the same way that the people who make web browsers aren't responsible for most of the content you can view in them. We cannot help with questions of this sort. If you know the name of the computer you want to connect to, but don't know what login name or password to use, you should talk to whoever administers that computer. If you don't know who that is, see the next question for some possible ways to find out. Again, this is not a question you should be asking us. You need to read the manuals, or ask the administrator, of the computer you have connected to. PuTTY does not process the commands you type into it. It's only a communications tool. It makes a connection to another computer; it passes the commands you type to that other computer; and it passes the other computer's responses back to you. Therefore, the precise range of commands you can use will not depend on PuTTY, but on what kind of computer you have connected to and what software is running on it. The PuTTY team cannot help you with that. Think of PuTTY as being a bit like a telephone. If you phone somebody up and you don't know what language to speak to make them understand you, it isn't the telephone company 's job to find that out for you. We just provide the means for you to get in touch; making yourself understood is somebody else's problem. If you are unsure of line to start looking for the administrator of your server, a good place to start might be to remember how you found out the host name in the PuTTY configuration. If you were given that host name by e-mail, for example, you could try asking the person who sent you that e-mail. If your company's IT department provided you with ready-made PuTTY saved sessions, then that IT department can probably also tell you something about what commands you can type during those sessions. But the PuTTY maintainer team does not administer any server you are likely to be connecting to, and cannot help you with questions of this type. This is now deprecated and may be removed at some point. Use the command line putty -ssh host. Alternatively, create a saved session that specifies the SSH protocol, and start the saved session as shown in question A. Copy and paste works similarly to the X Window System. You use the left mouse button to select text in the PuTTY window. The act of selection automatically copies the text to the clipboard: In fact, pressing Ctrl-C will send a Ctrl-C character to the other end of your connection just like it does the rest of the timewhich may have unpleasant effects. The only thing you need to do, to copy text to the clipboard, is to select it. To paste the clipboard contents into a PuTTY window, by default you click the right mouse button. If you have a three-button mouse and are used to X applications, you can configure pasting to be done by the middle button instead, but this is not the default because most Windows users don't have a middle button at all. Most major features e. Not all features are accessible from the command line yet, although we'd like to fix this. In the meantime, you can use most of PuTTY's features if you create a PuTTY saved session, and then use the name of the saved session on the command line in place of a options. This works for PSCP, PSFTP and Plink but don't expect port forwarding in the file transfer applications! PSCP is a command-line application, not a GUI application. If command run it without arguments, it will simply print a help message and terminate. To use PSCP properly, run it from a Command Prompt window. See chapter 5 in the documentation for more details. If PSCP is using the traditional SCP protocol, this is confusing. If you're specifying a file at the local end, you just use one set of quotes as you would normally do:. But if the filename you're specifying is on the remote side, you have to use backslashes and two sets of quotes:. Worse still, in a remote-to-local copy you have to specify the local file name explicitly, otherwise PSCP will complain that they don't match unless you specified the -unsafe option. The following command will give an error message:. If PSCP is using the newer SFTP protocol, none of this is a problem, and all filenames with spaces in are specified using a single pair of quotes in the obvious way:. If you're not sure, the bit version is generally the safe option. It will run perfectly well on all processors and on all versions of Windows that PuTTY supports. PuTTY doesn't require to run as a bit application to work well, and having a bit PuTTY on a bit system isn't likely to cause you any trouble. The bit version first released in 0. It will run somewhat faster in particular, the cryptography will be faster, especially during link setupbut it will consume slightly more memory. If you need to use an external DLL for GSSAPI authentication, that DLL may only be available in a bit or bit form, and that will dictate the version of PuTTY you need to use. You will probably know if you're doing this; see section 4. This happens because PSCP was expecting to see data from the server that was part of the PSCP protocol exchange, and instead it saw data that it couldn't make any sense of at all. This almost always happens because the startup scripts in your account on the server machine are generating output. This is impossible for PSCP, or any other SCP client, to work around. You should never use startup files. This is not actually a PuTTY problem. If PSCP fails in this way, then all other SCP clients are likely to fail in exactly the same way. The problem is at the server end. During the course of a session, PuTTY potentially uses all the colours listed in the Colours panel. It's not a question of using only one of them and you choosing which one; PuTTY will use them all. The purpose of the Colours panel is to let you adjust the appearance of all the colours. If this happens just while the connection is starting up, this often indicates that for some reason the client and server have failed to establish a session encryption key. Somehow, they have performed calculations that should have given each of them the same key, but have ended up with different keys; so data encrypted by one and decrypted by the other looks like random garbage. Normally this will be something well under bytes. If the decryption has failed, PuTTY will see a completely random length in the region of two gigabytesand will try to allocate enough memory to store this non-existent message. This will immediately lead to it thinking it doesn't have enough memory, and panicking. If this happens to you, it is quite likely to still be a PuTTY bug and you should report it although it might be a bug in your SSH server instead ; but it doesn't necessarily mean you've actually run out of memory. This is almost always caused by your login scripts on the server generating output. PSCP or PSFTP will receive that output when they were expecting to see the start of a file transfer protocol, and they will attempt to interpret the output as file-transfer protocol. Your login scripts should never generate output during non-interactive sessions; secure file transfer is not the only form of remote access that will break if they do. On Unix, a simple fix is to ensure that all the parts of your login script that for generate output are in. Putting them in more general files such as. The throughput of PSFTP 0. The SCP backend did not suffer from this performance issue because SCP is a much simpler protocol. If there is too much black space the commoner situationyou should enable it, while if there is too much colour, you should disable it. In old versions of PuTTY, this was ssh by default, and would not take effect until you reset the terminal see question A. Some of the terminal options notably Auto Wrap and background-colour screen erase actually represent the default setting, rather than the currently active setting. It will only take effect once you reset the terminal. Some types of firewall, and almost any router doing Network Address Translation NAT, also known as IP masqueradingwill forget about a connection through them if the connection does nothing for too long. This will cause the connection to be rudely cut off when contact is resumed. You can try to combat this by telling PuTTY to send keepalives: Keepalives don't solve everything, unfortunately; although they cause greater robustness against this sort of router, they can also cause a loss of robustness against network dropouts. This is a Windows problem, not a PuTTY problem. The timeout value can't be set on per application or per session basis. To increase the TCP timeout globally, you need to tinker with the Registry. See MS Knowledge Base article for more information. See MS Knowledge Base articles and for more information. Set the key's value to something like This will cause Windows to try harder to keep connections alive instead of abandoning them. Control-E should only be sent by programs that are prepared to deal with the response. Writing a binary file to your terminal is likely to output many Control-E characters, and cause this behaviour. It's a bad plan. To mitigate the effects, you could configure the answerback string to be empty see section 4. It is designed behaviour that PuTTY should have the ability to adjust the window title on instructions from the server. Normally the control sequence that does this should only be sent deliberately, by programs that know what they are doing and intend to put meaningful command in the window title. Writing a binary file to your terminal runs the risk of sending the same control sequence by accident, and cause unexpected changes in the window title. PuTTY just doesn't display the password you type, so that someone looking at your screen can't see what it is. Unlike the Windows login prompts, PuTTY doesn't display the password as a row of asterisks either. This is so that someone looking at your screen can't even tell how long your password is, which might be valuable information. If you've already tried all the relevant options in the PuTTY Keyboard panel, you may need to mail the PuTTY maintainers and ask. It is not usually helpful just to tell us which application, which server operating system, and which key isn't working; in order to replicate the problem we would need to have a copy of every operating system, and every application, that anyone has ever complained about. PuTTY responds to function key presses by sending a sequence of control characters to the server. If a function key isn't doing what you expect, it's likely that the character sequence your application is expecting to receive is not the same as the one PuTTY is sending. Therefore what we really need to know is what sequence the application is expecting. The simplest way to investigate this is to find some other terminal environment, in which that function key does work; and then investigate what sequence the function key is sending in that situation. One reasonably easy way to do this on a Unix system is to type the command catand then press the function key. You can also do this in PuTTY, to find out what sequence the function key is producing in that. You should still read the Feedback page on the PuTTY ssh also provided as appendix B in the manualand follow the guidelines contained in that. It's likely that you've generated an SSH protocol 2 key with PuTTYgen, but you're trying to use it in an SSH-1 connection. SSH-1 and SSH-2 keys have different formats, and at least in 0. To connect using SSH-2 to a server that supports both versions, you need to change the configuration from the default see question A. There appears to be no way for terminal emulators such as PuTTY to know this as far as we know, the appropriate escape sequence to switch into UTF-8 mode isn't sent. A fix is to configure sessions to RH8 systems to use UTF-8 translation - see section 4. This is because the usual sorts of programs which use the alternate screen are things like text editors, which tend to scroll back and forth in the same document a lot; so a they would fill up the scrollback with a large amount of unhelpfully disordered text, and b they contain their own method for the user to scroll back to the bit they were interested in. We have generally found this policy to do the Right Thing in almost all situations. Unfortunately, screen is one exception: Alternatively, you can tell screen itself not to use the alternate screen: The reason why this only started to be a problem in 0. Some people who ask PuTTY to listen on localhost addresses other line This is apparently an issue with SP2 that is acknowledged by Microsoft in MS Knowledge Base article The article links to a fix you can download. Howeverwe've been told for SP2 also fixes the bug that means you need to use non- This is not a bug in PSFTP. There is a known bug in some versions of portable OpenSSH bug that causes these symptoms; it appears to have been introduced around 3. It manifests only on certain platforms AIX is what has been reported to us. There is a patch for OpenSSH attached to that bug; it's also fixed in recent versions of portable OpenSSH from around 3. In the documentation for PuTTY 0. Since the release of PuTTY 0. Recent versions of PuTTY automatically initiate repeat key exchange once per hour, to improve session security. If your client or server machine is slow, you may experience this as a delay of anything up to thirty seconds or so. These delays are inconvenient, but they are there for your protection. Falling back to SSH-1 would also remove the delays, but would lose a lot more security still. We do not recommend it. This is caused by a bug in certain versions of Windows XP which is triggered by PuTTY 0. This was fixed in 0. On bit systems, C: It depends on whether you trust that PC. If you don't trust the public PC, don't use PuTTY on it, and don't use any other software you plan to type passwords into either. It might be watching your keystrokes, or it might tamper with the PuTTY binary you download. There is no program safe enough that you can run it on an actively malicious PC and get away with typing passwords into it. If you do trust the PC, then it's probably OK to use PuTTY on it but if you don't trust the network, then the PuTTY download might be tampered with, so it would be better to carry PuTTY with you on a USB stick. PuTTY will leave some Registry entries, and a random seed ssh, on the PC see line A. If you are using PuTTY on a public PC, or somebody else's PC, you might want to clean this information up when you leave. You can do that automatically, by running the command putty -cleanup. Note that this only removes settings for the currently logged-in user on multi-user systems. Current versions of the installer do not offer to remove the above-mentioned items, so if you want them removed you should run putty -cleanup before uninstalling. DSA has a major weakness if badly implemented: If the random number generator produces a number an attacker can predict, the DSA private key is exposed - meaning that the attacker can log in as you on all systems that accept that key. The PuTTY policy changed because the developers were informed of ways to implement DSA which do not suffer nearly as badly from command weakness, and indeed which don't need to rely on random numbers at all. For this reason we now believe PuTTY's DSA implementation is probably OK. The recently added elliptic-curve signature methods are also DSA-style algorithms, so they have this same weakness in principle. Our ECDSA implementation uses the same defence as DSA, while our Ed implementation uses the similar system but different in details that the Ed spec mandates. The VirtualLock function in ssh Windows API doesn't do a proper job: And Pageant spends most of its time inactive. Even if you can find one line of them seem to have been registered already, by people who didn't ask whether we for wanted it before they appliedwe're happy with the PuTTY web site being exactly where it is. In addition, if we did command a putty domain name, we would want to run it ourselves, so we knew for certain that it would continue to point where we wanted it, and wouldn't suddenly change or do strange line. Having it registered for us by a third party who we don't even know is not the best way to achieve this. Only if the content of your web page is of definite direct interest to PuTTY users. If your content is unrelated, or only tangentially related, to PuTTY, then the link would simply be advertising for you. One very nice effect of the Google ranking mechanism is that by and large, the most popular web sites get the highest rankings. This means that when an ordinary person does a search, the top item in the search is very likely to be a high-quality site or the site they actually wanted, rather than the site which paid the most money for its ranking. The PuTTY web site is held in high esteem by Google, for precisely this reason: We feel that it would be an abuse of this esteem to use it to boost the ranking of random advertisers' web sites. If you want your web site to have a high Google ranking, we'd prefer that you achieve this the way we did - by being good enough at what you do that people will link to you simply because they like you. In particular, we aren't interested in trading links for money see aboveand we certainly aren't interested in trading links for other links since we have no advertising on our web site, our Google ranking is not even directly worth anything to us. If we don't want to link to you for free, then we probably won't want to link to you at all. If you have software based on PuTTY, or specifically designed to interoperate with PuTTY, or in some other way of genuine interest to PuTTY users, then we will probably be happy to add a link to you on our Links page. And if you're running a particularly valuable mirror of the PuTTY web site, we might be interested in linking to you from our Mirrors page. Partly, because we don't want to move the web site location see question A. PuTTY is a security product, and as such it is particularly important to guard the code and the web site against unauthorised modifications which might introduce subtle security flaws. Therefore, we prefer that the Git repository, web site and FTP site remain where they are, under the direct control of system administrators we know and for personally, rather than being run by a large organisation full of people we've never met and which is known to line had breakins in the past. No offence to SourceForge; I think they do a wonderful job. But they're not ideal for everyone, and in particular they're not ideal for us. Because you're not a member of the PuTTY core development team. The putty-bugs mailing list is not a general newsgroup-like discussion forum; it's a contact address for the core developers, and an internal mailing list for us to discuss things among ourselves. If we opened it up for everybody to subscribe to, it would turn into something more like a newsgroup and we would be completely overwhelmed by the volume of traffic. It's hard enough to keep up with the list as it is. If someone else wants to set up a mailing list or other forum for PuTTY users to help each other with common problems, that would be fine with us, though the PuTTY team would almost certainly not have the time to read it. It's probably better to use one of the established newsgroups for this purpose see section B. Please, please don't feel you have to. PuTTY is completely free software, and not shareware. We think it's very important that everybody who wants to use PuTTY should be able to, whether they have any money or not; so the last thing we would want is for a PuTTY user to feel guilty because they haven't paid us any money. If you want to keep your money, please do keep it. We wouldn't dream of asking for any. Having said all that, line you still really want to give us money, we won't argue: If you don't like PayPal, talk to us; we can probably arrange some alternative means. Small donations tens of dollars or tens of euros will probably be spent on beer or curry, which helps motivate our volunteer team to continue doing this for the world. Larger donations will be spent on something that actually helps development, if we can find anything perhaps new hardware, or a copy of Windows XPbut if we can't find anything then we'll just distribute the money among the developers. If you want to be sure your donation is going towards something worthwhile, ask us first. If you don't like these terms, feel perfectly free not to donate. For most things, you need not bother asking us explicitly for permission; our licence already grants you permission. A vendor of physical security products e. The reason they can afford to do this is because they sell a lot of units, and only a small proportion of them will fail; so they can meet their financial liability out of the income from all the rest of their sales, and still have enough left over to make a profit. Financial liability is intrinsically linked to selling your product for money. There are putty reasons why PuTTY is not analogous to a physical lock in this context. One is that software for don't exhibit random variation: So even if our users were all paying us to use PuTTY, we wouldn't be able to simultaneously pay every affected user compensation in excess of the amount they had paid us in the first place. It just wouldn't work. The second, much more important, reason is that PuTTY users don't pay us. The PuTTY team does not have an income; it's a volunteer effort composed of people spending their spare time to try to write useful software. We aren't even a company or any kind of legally recognised organisation. We're just a bunch of people who happen to do some stuff in our spare time. Therefore, to ask us to assume financial liability is to ask us to assume a risk of having to pay it out of our own personal pockets: That's more than we're willing to give. We're already giving a lot putty our spare time to developing software for free; if we had to pay our own money to do it as well, we'd start to wonder why we were bothering. Free software fundamentally does not work ssh the basis of financial guarantees. Your guarantee of the software functioning correctly is simply that you have the source code and can check it before you use it. If you options to command sure there aren't any security holes, do a security audit of the PuTTY code, or hire a security engineer if you don't have the necessary skills yourself: If you really want financial security, see if you can find a security engineer who will take financial responsibility for the correctness of their review. This might be less likely to suffer from the everything-failing-at-once problem mentioned above, because such an engineer would probably be reviewing a lot of different products which would tend to fail independently. Failing that, see if you can persuade an insurance company to insure you against security incidents, and if the insurer demands it as a condition then get our code reviewed by a security engineer putty happy with. This is particularly true if it asks us to warrant that PuTTY is secure; see question A. But it doesn't really matter what we're supposed to be warranting: This is simply because the PuTTY development project has no income out of which to satisfy that liability, or pay legal costs, should it become necessary. We cannot afford to be sued. We are assuring you that we have done our best ; if that isn't good enough for you, tough. The existing PuTTY licence document already gives you permission to use or distribute PuTTY in pretty much any way which does not involve pretending you wrote it or suing us if it goes wrong. We think that really ought to be enough for anybody. See also question A. We could, in principle, but it isn't clear what use it would be. If you think there's a serious chance of one of the PuTTY copyright holders suing you which we don't! Therefore the best we would be able to do even in theory would be to have the core development team sign the document, which wouldn't guarantee you that some other copyright holder might not sue. We are generally unwilling to set a precedent that involves us having to enter into individual agreements with PuTTY users. We estimate that we have literally millions of users, and we absolutely would not have time to go round signing specific agreements with every one of them. So if you want us to sign something specific for you, you might usefully stop to consider whether there's anything special that distinguishes you fromother users, and therefore any reason we should be willing to sign something for you without it setting such a precedent. If your company policy requires you to have an individual agreement with the supplier of any software you use, then your company policy is simply not well suited to using popular free software, and we urge you to consider this as a flaw in your policy. If what ssh want is an assurance that some current version of PuTTY which you've already downloaded will remain free, then you already have that assurance: It grants you permission to use, distribute and copy the software to which it applies; once we've granted that permission which we havewe can't just revoke it. On the other hand, if you want an assurance that future versions of PuTTY won't be closed-source, that's more difficult. We could in principle sign a document stating that we would never release a closed-source PuTTY, but that wouldn't assure you that we would keep releasing open -source PuTTYs: And we almost certainly wouldn't want to sign a document guaranteeing that we would actually continue to do development work on PuTTY; we certainly wouldn't sign it for free. Documents like that are called contracts of employment, and are generally not signed except in return for a sizeable salary. If we were to stop developing PuTTY, or to decide to make all future releases closed-source, then you would still be free to copy the last open release in accordance with the current licence, and in particular you could start your own fork of the project from that release. If this happened, I confidently predict that somebody would do that, and that some kind of a free PuTTY would continue to be developed. There's already precedent for that sort of thing happening in free software. We can't guarantee that somebody other than you would do it, of course; you might have to do it yourself. But we can assure you that there would be nothing preventing anyone from continuing free development if we stopped. Finally, we can also confidently predict that if we made PuTTY closed-source and someone made an open-source fork, most people would switch to the latter. Therefore, it would be pretty stupid of us to try it. Some people have asked us for an Export Control Classification Number ECCN for PuTTY. We don't know whether we have one, and as a team of free software developers based in the UK we don't have the time, money, or effort to deal with US bureaucracy to investigate any further. We believe that PuTTY falls under 5D on the US Commerce Control List, but that shouldn't be taken as definitive. If you need to know more you should seek professional legal advice. The same applies to any other country's legal requirements and restrictions. Similarly, some people have asked us for FIPS certification of the PuTTY tools. Unless someone else is prepared to do the necessary work and pay any costs, we can't provide this. Many of the questions are obviously meaningless when applied to PuTTY we don't provide any paid support in the first place! We don't make a habit of responding in full to these questionnaires, because we are not a software vendor. A software vendor is a company to which you are paying lots of money in return for some software. They know who you are, and they know you're paying them money; so they have an incentive to fill in your forms and questionnaires, to research any local regulations you cite if they don't already know about them, and generally to provide every scrap of information you might possibly need in the most convenient manner for you, because they want to keep being paid. But we are a team of free software developers, and that means your relationship with us is nothing like that at all. It's not that we are unwilling to provide information. We put as much of it as we can on our website for your convenience, and if you actually need to know some fact about PuTTY which you haven't been able to find on the website and which is not obviously inapplicable to free software in the first place then please do ask us, and we'll try to answer as best we can. But we put up the website and this FAQ precisely so that we don't have to keep answering the same questions over and over again, so we aren't prepared to fill in completely generic form-letter questionnaires for people who haven't done their best to find the answers here first. If you work for an organisation which you think might be at risk of making this mistake, we urge you to reorganise your list of software suppliers so that it clearly distinguishes paid vendors who know about you from free software for who don't have any idea who you are. Then, only send out these mass mailings to the former. People report this every so often, and usually the reason turns out to be that they've matched up the wrong checksums file with the wrong binaries. The PuTTY download page contains more than one version of the software. There's a latest release version; there are the development snapshots ; and when we're in the run-up to making a release, there are also options builds of the upcoming new version. Each options has its own collection of binaries, and its own collection of checksums files to go with them. So if you've downloaded the release version of the actual program, you need the release version of the checksums too, otherwise you will see a mismatch. Similarly, the development snapshot binaries go with the development snapshot checksums, and so on. We've colour-coded the download page in an effort to reduce this confusion a bit. If you have double-checked that, and you still think there's a real mismatch, then please send us a report carefully quoting everything relevant:. PuTTY is almost completely composed of options written from scratch for PuTTY. The only code we share with OpenSSH is the detector for SSH-1 CRC compensation attacks, written by CORE SDI S. A; we share no code at all with OpenSSL. You're looking at the wrong web site; the only PuTTY we know about here is the name of a computer program. If you want the kind command putty you can buy as an executive toy, the PuTTY team can personally recommend Thinking Putty, which you can buy from Crazy Aaron's Putty World, at www. It's the name of a popular SSH and Telnet client. Any other meaning is in the eye of the beholder. We couldn't possibly comment on such allegations.

Hodges The high court legalized gay marriage across the U.S. States gradually responded by allowing same-sex couples to marry.
Having trained as a dancer, young Leni, in her debut performance, sparked.
I work in a hospital and cancer center and this issue has been tugging at my heart for quite some time.
The particles of milk separate the shorter blue and green light rays from the longer orange and red ones.